
No need to worry about protocols and message brokerage anymore. Easily get your data via webhooks to any endpoint by using our portal or API.
We support a lot of different protocols out of the box and you can even use them in parallel.




Need help selecting the right protocol?
What is the difference between TCP and UDP? How does LWM2M, MQTT or CoAP work and what are the respective advantages and disadvantages?
Send all the messages you want and how you want, we will deliver them to you.
You’ve got mail payload!
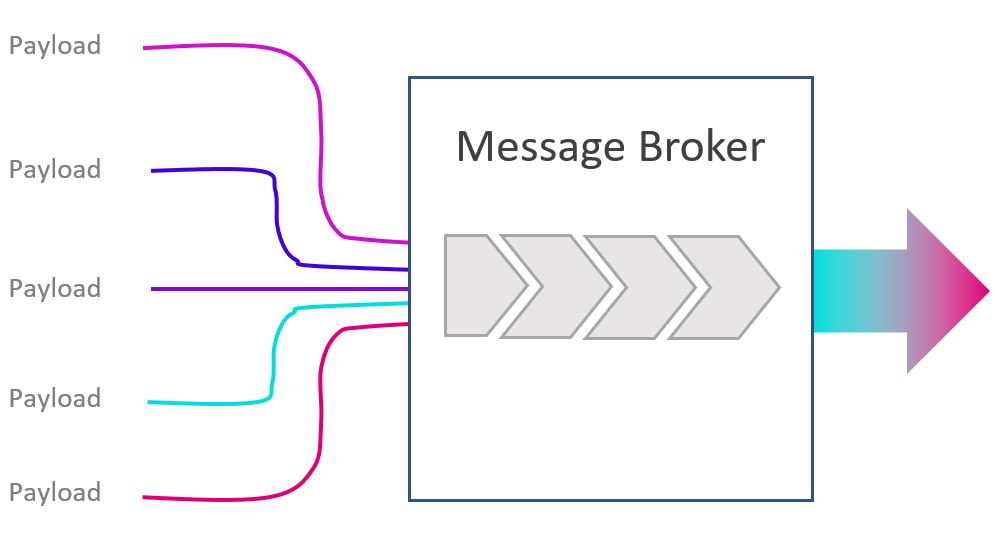
Our message broker converts the messages from your various messaging protocol flavors into a uniform format for the receiving endpoint. The broker validates, stores, routes, and delivers the messages to your pre-defined destination.
Register your devices in minutes, manage them in projects, and share access with your team.

Simple to use
Real-time data
Platform Integration

We have huge library of by step by step webhook integration with you favorite IoT platforms.
